As shown in the last blog, Microsoft prepopulated all Microsoft apps that have the Intune SDK integrated. As we all know, there are a lot more apps that are available in the Apple iTunes store and the Google Play store that supports the App Protection Policies. (see a complete list of apps that support App Protection Policies here)
So let’s see how we are able to add those apps to the Intune on Azure and how we can arrange that they are also managed by the App Protection Policies.
Adding apps
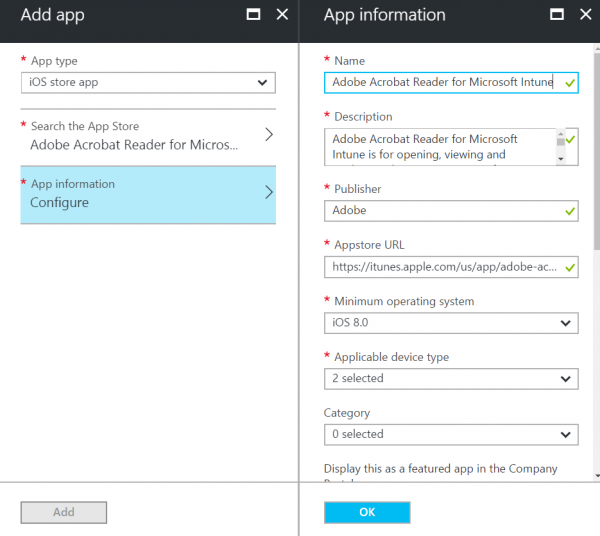
Adding apps in Intune on Azure is way more easy than on the old Silverlight Console. For iOS it cannot made easier than is created now in the new Intune on Azure portal. If you go to Intune >> Mobile Apps >> App and the click on Add, you have the option to select iOS Store as the App type.
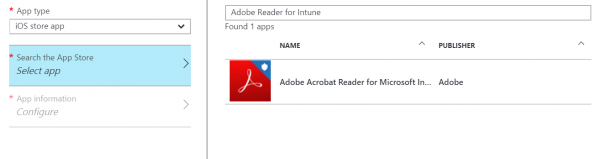
If we click Search the App Store and search for instance for Adobe Acrobat for Intune we will see one result.
Next we can select this app and click OK to add it and click on App Information we see that all information is prepopulated by Intune with the information that is available in the iTunes store. Microsoft is using the API that Apple has created to gather information from the iTunes app store. By clicking OK and Add you have created the app, how easy is that? 😉
For Android this is unfortunately not the case, we still need to find the app in the Google Play Store and copy the URL to the Intune Portal. Also we need to download the icons and add all the metadata ourselves.
Unfortunately Google did not make an IPA like Apple did L Maybe they have also something called User Voice to request our features 😉
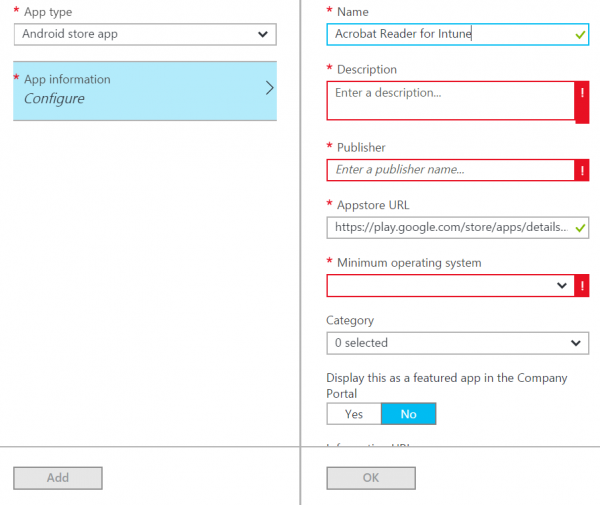
We need to add the information and the URL ourselves.
Targeting App Protection Policies to new apps
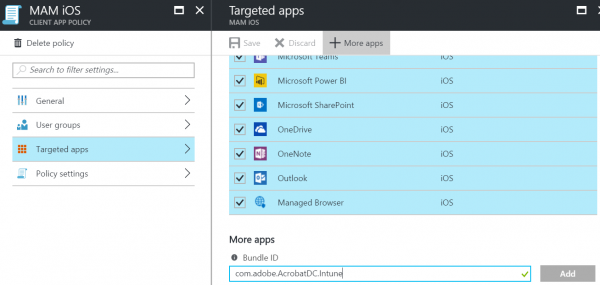
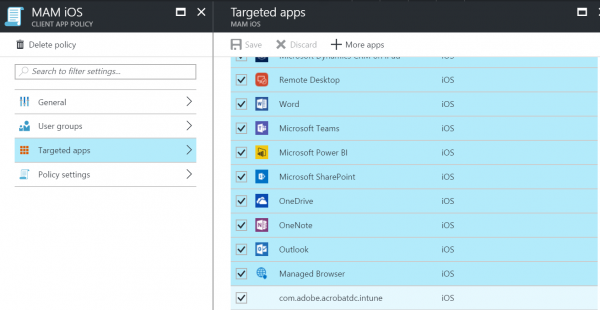
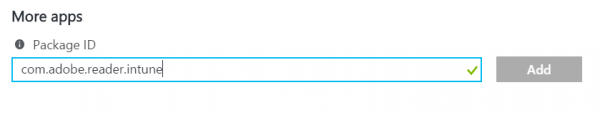
Unfortunately the new Intune Portal on Azure, at least for now, is not able to detect if the Apps have the Intune SDK integrated like we were used to in the Silverlight portal. The only way of doing this is to add the Bundle ID of the iOS app or the Package ID for Android.
This can be done by going to Intune >> Mobile Apps >> App Protection Policies >> <iOS App Protection Policy> >> Targeted App and then click on More Apps.
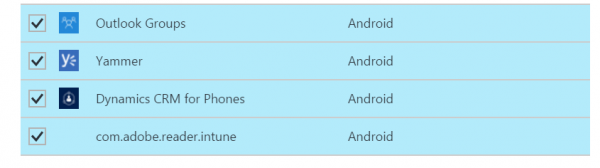
For Android we need to add not the Bundle ID, but the Package ID. We can do this the same way by using the More Apps option in the Targeted apps blade of the Android App Protection Policy.
So how do we get the Bundle ID and Package IDs from App stores?
Again two different ways of gathering the information we need above. For iOS we can add a column called Bundle to the list of Apps in the Intune >> Mobile Apps >> Apps blade.
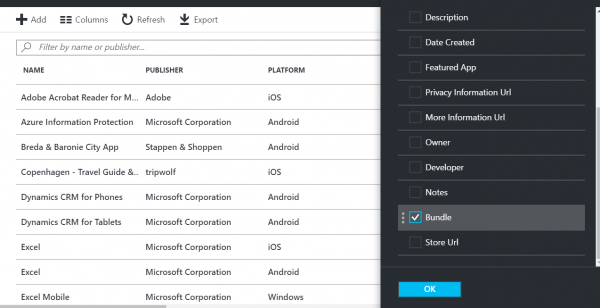
By adding the Bundle column we are able to identify the bundle ID of the iOS app. Copy this value and use it while adding the app in the iOS App Protection Policy.

For Android we need to search the app in the Google Play store, and then the only thing we need to do is note the ID listed in the URL of the App in the Browser like shown below.
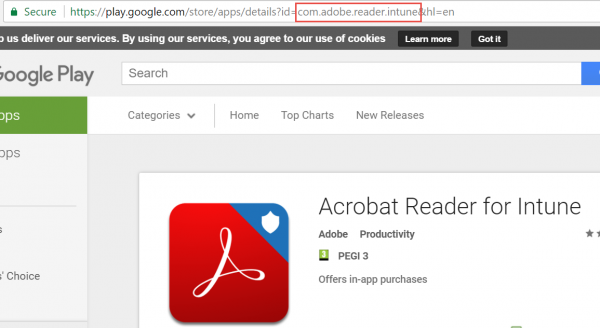
Copying the value of the ID in the URL and pasting it while adding the Package ID in the Android App Protection Policy allows us also to target this added app, just like with iOS.
Note:
Currently the Intune Portal on Azure is still in preview, when things like described above I will either change this blog or refer to the new blog below.
Till next time!



The “Bundle ID” column is now called “App Identifier”.
Thanks Peter!