Since Configuration Manager 1610 and the latest Intune release a new feature became available which allows you to switch MDM authority without needing to contact Microsoft Support and without needing to reenroll the enrolled mobile devices.
In this blogpost I want to cover the experience of switching from Configuration Manager Hybrid (connected with Intune) to Intune stand alone. In my next blogpost I will cover how to switch from Intune stand alone to Intune Hybrid.
Let’s see how this process works.
Little bit of background
When using Office 365, Microsoft Intune or System Center Configuration Manager together with Microsoft Intune to manage your mobile devices a fundamental choice needs to made when starting configuring the service.

You need to either configure the MDM Authority to Office 365 (+Intune), Microsoft Intune or Configuration Manager. Switching the MDM authority from Intune standalone or Intune Hybrid could not be done easily, Microsoft Support needed to be contacted, all devices needed to be unenrolled and all resources needed to be removed… Until now, Microsoft invested to make the process of switching the MDM authority super easy and without needing to reenroll every device.
Preparation
First of all, we need to take into account that resources created in Configuration Manager and deployed to mobile devices like configuration profiles (policies), VPN profiles, WiFi profiles, applications, certificate profiles and more, need to be recreated after making the switch. Until making the switch to Intune standalone, the current Intune on Azure portal cannot be used.

This is because the fact that the new Intune on Azure portal is still in preview, this will most likely to be fixed when the portal is general available. (will update this when it is fixed) The old Silverlight portal is able to populate the right MDM Authority:

Be sure to approach this switch as a small project where you first document your current environment and plan how and when to perform the switch, your work is not finished after making the switch!
Document current environment
Document your current environment and identify the following;
Platform support
Document what platforms you are supporting and what needs to be done to make sure that reenrollment of the device is not necessary.
iOS / MacOs
For iOS and MacOs devices the same Apple Push Notification (APNs) certificate needs to be configured in Microsoft Intune standalone as soon as possible after the switch. Creating a new APNs certificate will result in the fact that all iOS and MacOs devices need to be reenrolled, so be sure to document the Apple ID and be sure that you know what APNs certificate needs to be renewed.

The VPN tokens you added will be available in the new Intune on Azure portal.
Android
For Android nothing special needs to be done. Android for Work integration is configured in the Microsoft Intune on Azure portal.
Windows
Nothing special needs to be done, be sure to import the signing certificates if used. The Windows Store for Business needs to be reconfigured in Microsoft Intune, more on this in a later blog.
Resources and current settings
Document what configurations are deployed to the mobile devices and document for what platforms they are created and deployed. Make a list of all resources with all settings for the following objects;
- VPN Profile
- WiFi Profile
- Certificate Profiles
- Configuration Items and Configuration Baselines
- Mobile Application Management policies
- Mobile Application Configuration policies
- Compliance Policies
- Windows Hello for Business
- Terms and conditions
- Conditional Access
- Third party Integration
- Applications
For Applications be sure to identify what kind of apps you are deploying, Apps from the store, via the business store (Android for Work, VPP or Windows Store for Business) or native LOB apps. Also note down if the Apps are available or required for the users.
Where are the resources deployed to? What Collections are used?
Investigate what collections are used to deploy the resources and applications to. For instance; note down what Active Directory Groups are member of the collections, or what direct memberships do exist? In Intune you are going to assign your resources to Azure AD groups, which can be the following;
- Assigned groups (users or devices manually assigned to groups)
- Synced groups (user groups synchronized from the local Active Directory)
- Dynamic Device groups (dynamic groups based on a device query)
- Dynamic User groups (dynamic groups based on a user query)
Start making a translation of your collections to Azure AD groups on paper.
Identity what need to be recreated
After document the current environment you need to recreate the following profiles after making the MDM authority switch.
- VPN Profile
- WiFi Profile
- Certificate Profiles
- Configuration Items and Configuration Baselines
- Mobile Application Management policies
- Mobile Application Configuration policies
- Compliance Policies
- Windows Hello for Business
- Terms and conditions
- Applications
The following is configured already in Azure AD and Intune;
- Conditional Access
- Android for Work configuration
- VPP support (am not able to check DEP support)
- Third-party integration like Lookout and Skycure.
- All App Policies and App Configuration under Intune mobile application management node in the Azure portal. (MAM without enrollment support)
Perform the switch
Before performing the switch you need to remove  the following from Configuration Manager;
- Remove the Enrollment Manager
- Remove the device categories
The switch can performed by doing the following;
- In the Configuration Manager console, go to Administration > Cloud Services > Microsoft Intune Subscriptions and select the Microsoft Intune Subscription. Click Delete.
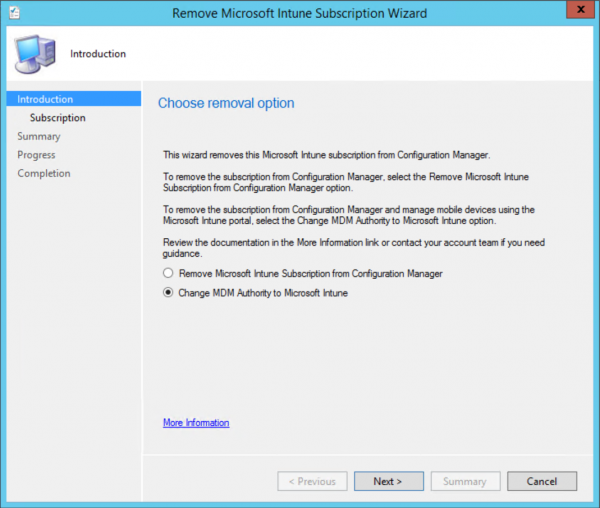
- Select Change MDM Authority to Microsoft Intune and click Next
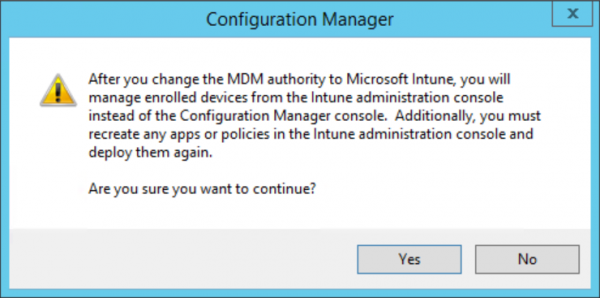
- Click Yes and sign in with your Organizational account.
- Click Next, Next, Done.
After the switch has been made, the Intune related logfiles in Configuration Manager will indicate the following: Site has no Intune subscription.
Looking in the portal you will see that the MDM Authority is being reset and that it needs to be configured to Microsoft Intune.


After setting the MDM authority to Intune part one is done.
Prepare platform support and recreate resources
After making the switch each device holds up to 7 days to its policies, this way the devices stay secure and have the time to receive the information about the new MDM authority and the policies. Recreating the resources however needs to be done as soon as possible so that your devices stay secure!
Enable platform support
Be sure to renew the same APNs certificate as you have used in the Configuration Manager Hybrid environment.
Renewing the APNs certificate can be done in the new Intune on Azure portal via Intune >> Device Enrollment >> Apple Enrollment >> Apple MDM Push Certificate.
- Download your CSR
- Go to https://identity.apple.com/pushcert/ find the APNs certificate and click renew.
- Upload the CSR and download the new MDM_ Microsoft Corporation_Certificate.pem file
- Upload the new MDM_ Microsoft Corporation_Certificate.pem file in the Intune on Azure portal.

For Android and Windows Support the device platforms / restrictions can be changed here in the new Intune on Azure portal; Intune >> Device Enrollment >> Enrollment restrictions >> Device Type Restrictions.
Recreate and assign the resources
Find below notes about the different resources that need to be recreated, recreate the resources with the same name so that they are overwritten and that the new settings will be applied.
VPN, WiFi and Certificate Profiles
Recreate the VPN, WiFi and Certificate profiles and assign them to the (new) Azure AD groups. Make sure that the right profiles are available for your needs.
Configuration Items and Configuration Baselines
Translate the Configuration items to Device Restriction Profiles and recreate them per platform. Assign the policies to the Azure AD groups you identified earlier.

Compliance Policies
Translate the created compliance policies in Configuration Manager to compliance policies per platform. Intune on Azure does not support combining one compliance policy for all platforms in one.
Windows Hello for Business
Windows Hello for Business settings needs to be reconfigured to support Windows 10.

Terms and conditions
Create the new terms and conditions for the users, the users need to reaccept the terms and conditions after assigning it again to an Azure AD group.
Applications
In the new Intune on Azure portal all Microsoft apps that have the Intune SDK integrated are already added to Intune and ready for you to be assigned to the Azure AD groups. Line of Business apps need to be added again.

The App Configuration Policies and App Protection Policies (MAM policies) need also to be recreated and targeted to the Apps and assigned to a group of users.
The end result
After all resources are recreated and everything is assigned to the right Azure AD groups be sure to test if you are able to enroll devices. It can take up to 8 hours before the first already enrolled devices will notice the authority switch and get the new policies. You can trigger this by requesting the policies on the device, the device will show up after a while in the new Intune on Azure portal like shown below.

 |
 |
Like mentioned earlier, be sure to name the resources the same as the source environment so that your users not end up with double content.
VPP and Android for Work is already configured and available in the Intune portal.


Read also about the MDM authority switch here: https://docs.microsoft.com/en-us/sccm/mdm/deploy-use/change-mdm-authority#main
In the next blog about this subject I will switch the authority back to Configuration Manager hybrid. Always try this exercise first in a lab environment before performing the switch in production.
Stay tuned!



